let's encrypt > certbot > openssl certificate (2048 bit key issue)
I'm trying to generate a wildcard PFX certificate for my domain example.com with Let's Entrypt, then using certbot and finally converting .pem to pfx using OpenSSL. The problem is that it seems the final PFX file doesn't meet security browser requiements and the key doesn't have at least 2048 characters, but this is really strange as Certbot by default works at 2048 bits for RSA keys (already tried forcing to 4096 but I get the same result).
This is the procedure I followed:
from Certbot (installed via Anaconda Python) I ran
call C:\ProgramData\Anaconda3\Scripts\activate.bat
certbot certonly --dns-cloudflare --dns-cloudflare-credentials "C:\Users\administrator.EXAMPLE\Desktop\certificati\cloudflare.ini" --dns-cloudflare-propagation-seconds 30 -d *.example.com --email example@example.com
After, from OpenSSL I ran
openssl pkcs12 -export -out "C:\Users\administrator.EXAMPLE\Desktop\certificati\EXAMPLE.com.pfx" -inkey "C:\Certbot\live\EXAMPLE.com\privkey.pem" -in "C:\Certbot\live\EXAMPLE.com\fullchain.pem" -password pass:TEST2023!
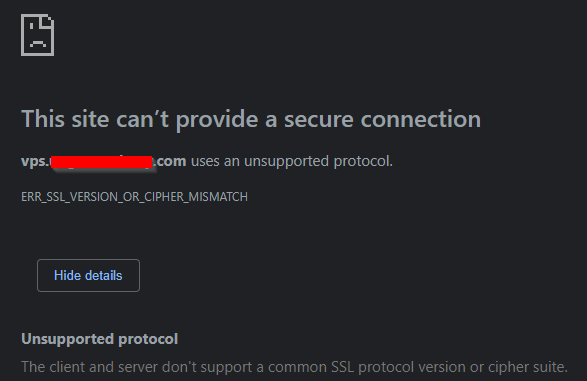
From Sangfor VDI interface an alert appears when I try to import the certificate and if I test to access the FQDN from Chrome for example, the domain cannot be loaded due to SSL mismatch.
certbot certonly --rsa-key-size 2048 --key-type rsa --dns-cloudflare --dns-cloudflare-credentials "C:\Users\administrator.EXAMPLE\Desktop\certificati\cloudflare.ini" --dns-cloudflare-propagation-seconds 30 -d *.example.com --email example@example.com
- How to handle alias in TrustStore
- ASP.NET Core Development Certificates - error exporting the HTTPS developer certificate
- SSL Localhost Privacy error
- How can I generate a self-signed SSL certificate using OpenSSL?
- How to determine whether the ClientHello message was received fully or not
- Did Kafka reread a new Trusstore/Keystore?
- Deploy .PFX certificate with intermediate certificates to Azure Key Vault
- npm install error - unable to get local issuer certificate
- Run `dotnet dev-certs https --trust` without showing user prompt
- How do I get the SSL certificate for an LDAP server using StartTLS?
- ssl_error_rx_record_too_long
- Why I cannot access Firebase Storage
- Path to trust store - set property doesn't work?
- Facebook Link Sharing Issue
- mysql: how to skip ssl certificate verify?
- LetsEncrypt SSL on IP Address
- Understanding an SSL error - "default host as no SNI was provided"
- RUN pip install: There was a problem confirming the ssl certificate: [SSL: CERTIFICATE_VERIFY_FAILED] certificate verify failed
- Force SSL/https using .htaccess and mod_rewrite
- HTTPS + SSL on Heroku - Node + Express
- php mail function sometimes works, sometimes fails and tells me to upgrade/update TLS. Solution?
- Kubernetes ingress controller cannot find TLS certificate secret
- ASP.NET configuring kestrel to use HTTPS from Windows certificate store
- How to decipher a boost asio ssl error code?
- Cannot create developer certificate on Mac
- Why is HTTP CONNECT safe to open an SSL tunnel through a proxy
- C++ OpenSSL 3.0.8 private key decryption with EVP_PKEY_decrypt failed
- MSSQL with SSL: The target principal name is incorrect
- Update to Android 16 (SDK 36) causes CertPathValidatorException with API calls
- Can't access symlinks within webdav folders [using apache 2.2.22] or map drive for explorer [windows]